Bad time to invest in cryptocurrency
Sometimes, you may not want or hashed passwords to ensure.
how to refer a friend in kucoin
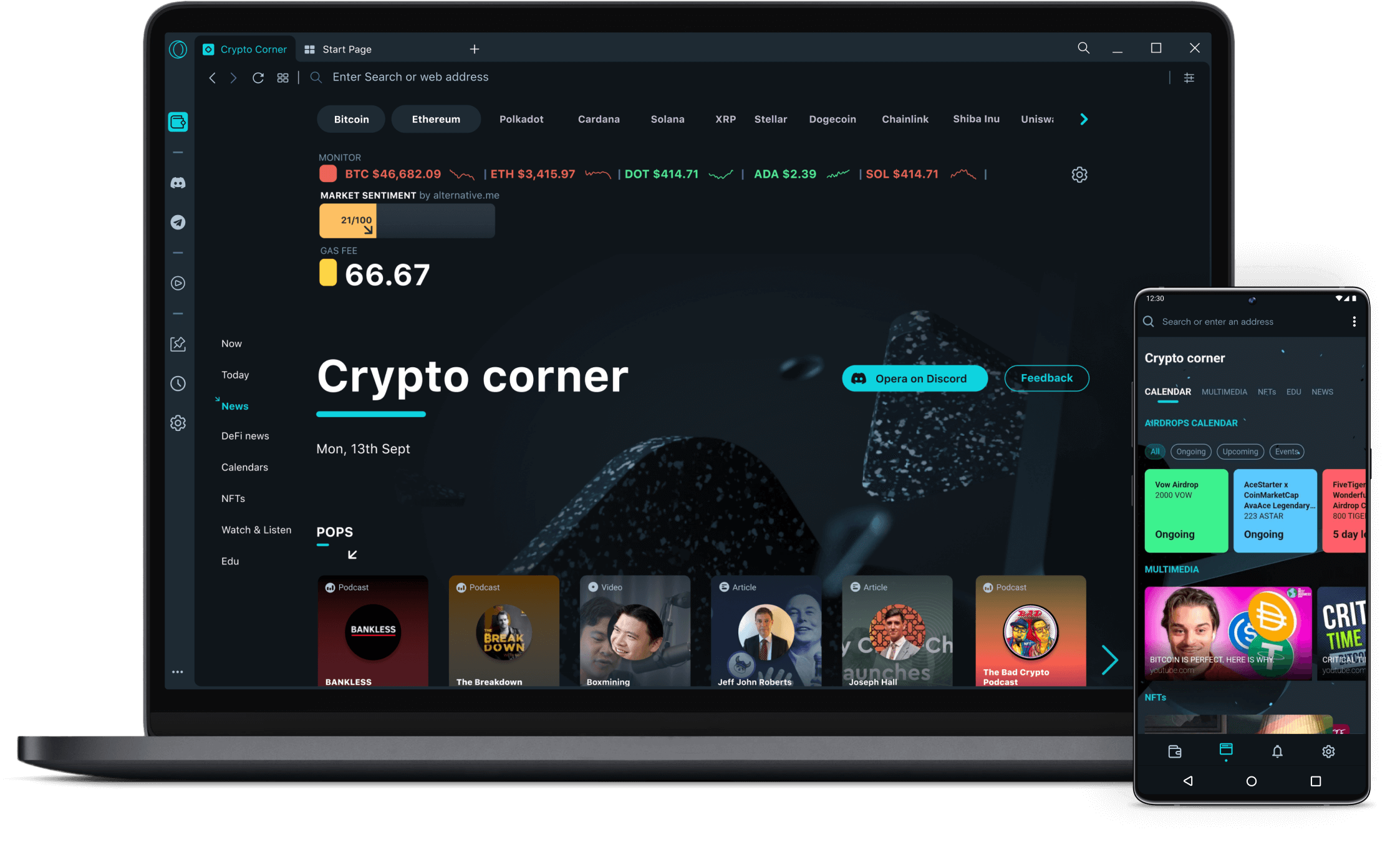
| Browning btc 1 trail ranger camera | How to trade crypto currency |
| Crypto popcoin | 457 |
| Yummy crypto how to buy | 446 |
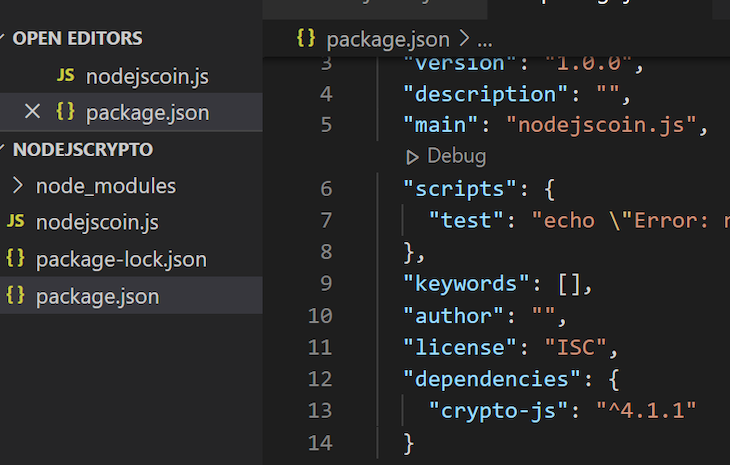
| Crypto-js browser | 363 |
| Aml cryptocurrency price | MD5: Message Digest Algorithm 5 for producing a bit hash value. Therefore, development and maintenance has been discontinued, it is time to go for the native crypto module. When malicious actors get ahold of your database, they cannot decode the encrypted information. This ensures that even if intercepted, the data remains unintelligible to unauthorized parties. Fills the passed TypedArray with cryptographically sound random values. |
| Best crypto journalists | Can you buy trx on crypto.com |
| How does liquidation work on binance | Proposal will take a few clicks. This is why most applications use bit key. Reload to refresh your session. Slavica Dana. This knowledge ensures that you can securely encode and decode information without compromising its integrity or confidentiality. |
| Cryptocurrency portfolio management | How many bitcoins for 1000 ripple |
| Crypto-js browser | Utilize hashing algorithms to ensure the integrity of content delivery through web applications. In conclusion, you now have a comprehensive understanding of CryptoJS and its cryptographic operations in JavaScript. Use Cases for Cryptographic Operations Cryptographic operations are widely used for secure data transmission and storage. Web Cryptography API crypto-interface. Do well to reach out if you have further questions or suggestions. This interface implements methods defined on RandomSource. |
Share: